Four keys to selecting safe mobile applications.
Mobile device security will be a hot button topic for years to come. Smartphones and tablets are only becoming more sophisticated, and with the emergence of wearables like Samsung and Apple watches and the continuous expansion of the Internet of Things (IoT), connections and communications between devices — and the data they generate — will only continue to multiply.
With this growth comes new challenges for security — and new opportunities for scammers and hackers.
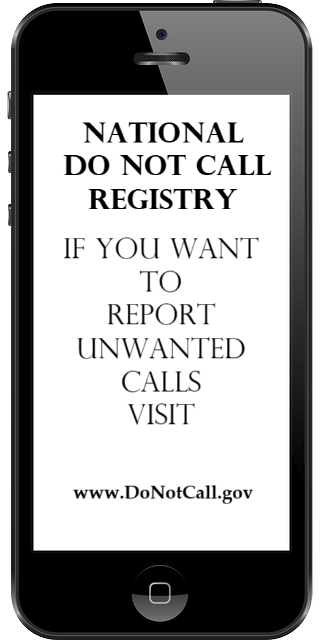
Phishing emails, smishing texts, unsecured Wi-Fi connections, and Bluetooth vulnerabilities are likely to come immediately to mind as far as threats associated with modern mobile devices. But it’s important to recognize that nearly every “smart” feature poses a risk to corporate and personal data.
- Sharing on social networking sites can give scammers insights into personal and business pursuits.
Four Mobile App Security Practices to Implement Today
Whether your organization supports a Bring Your Own Device (BYOD) policy or you are required to use a corporate device, it’s critical that you understand the best practices you can use to protect the business and personal data that is stored and shared through your smartphones and tablets.
Here are four simple, effective steps to follow before adding any mobile application to your device:
- Review the app’s download and update history.
Make sure you have a clear sense of what the app intended to do, how recently it was updated in the app store, and how many times it’s been downloaded.
- As a general rule, apps with fewer than 2,000 downloads are riskier, particularly if you don’t know much about them. The more an app is used by others, the more likely it is that problems and issues will come to light. Very recent updates (particularly those less than a week old) should be treated with caution; if possible, take a “wait and see” approach.
Read the Reviews
People commonly receive app recommendations from friends and family, but it’s important to read the reviews that are posted in the app store and online forums. It’s in these areas that you’re likely to gain insights into positives and negatives associated with app performance and functionality. As with many things in life, there’s strength in numbers; the more reviews there are, the more confident you can be in the information they share.
Understand the Permissions
App permissions can be a confusing business. Many different apps request many different permissions, and it can be hard to decipher the potential ramifications of downloading invasive apps. To complicate matters, there is no “one size fits all” approach to permissions; requests that make sense with one app could be totally out of bounds for another app.
Location tracking, access to contacts and calendars, the ability to send text messages, and control of your Internet connection are just some of the worrisome permissions requested by mobile apps. Online research can help you figure out the implications of these access requests and how certain permissions can negatively impact your privacy and data. Due diligence and footwork is the key to ensuring apps you download will have the least impact on the security of your device and the data it stores.
Check for Obvious Signs of Malware
You should steer clear of any apps that offer access to pirated, stolen, or risqué content. These kinds of apps can contain illegal materials, and all are risky because they tend to have hidden dangers, including malware. Beyond the malware you could add to your device, the app permissions granted to these kinds of apps could leave your device and its data vulnerable to cyber attackers.
We at SecureCyberNetwork are dedicated to providing you with the latest updates, tips, and expert advice to keep you safe in the digital world.
Your commitment to staying informed is about your safety, the safety of your loved ones, and the safety of our community.
Your involvement is powerful.